Smart Home Security in 2026
How to build a secure connected home
Smart Home Security
in 2026
Building a secure, connected home starts with structure—not devices.
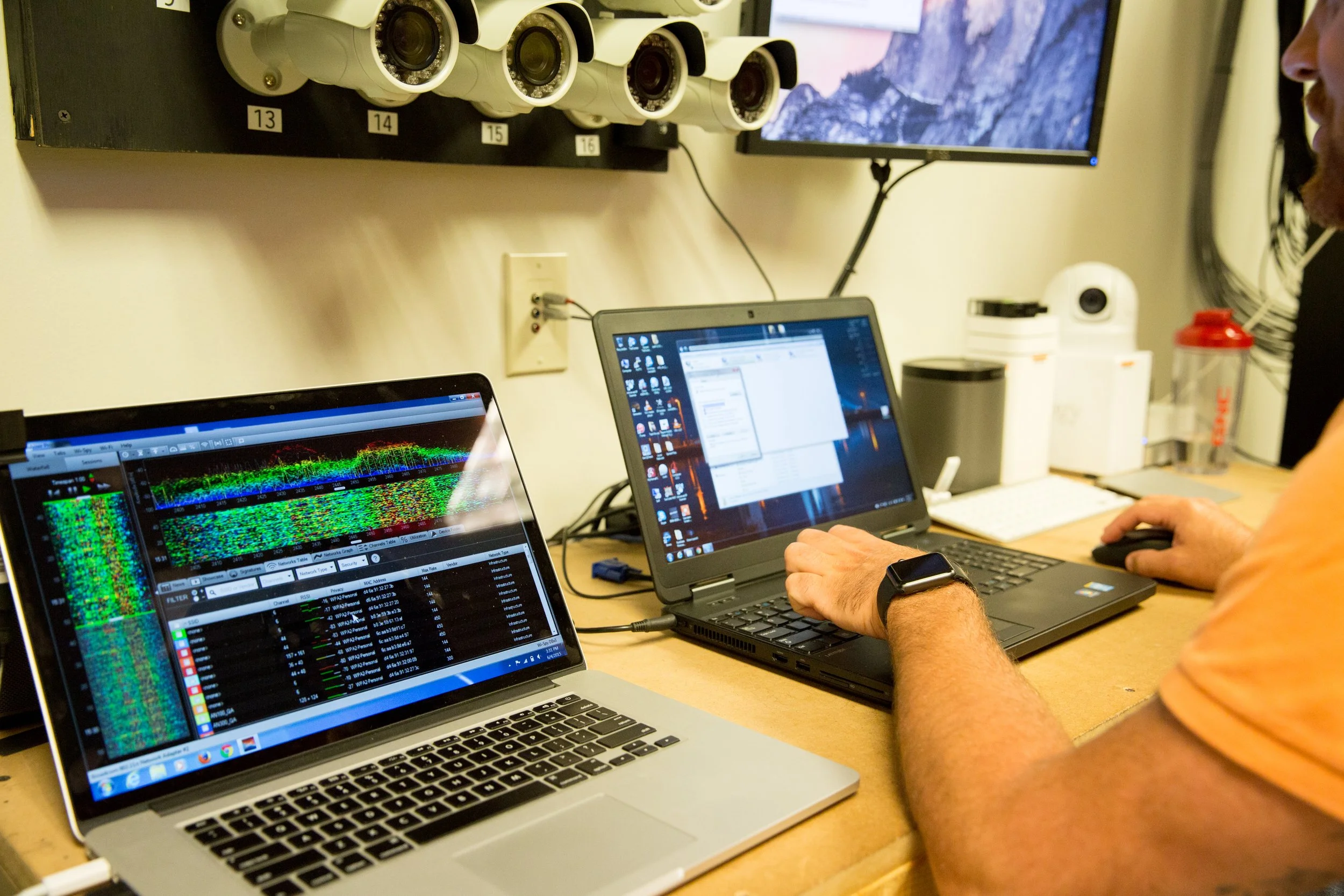
Smart home security is no longer limited to cameras and alarms. It’s about how the entire system is designed, connected, and maintained over time.
Lighting, climate, surveillance, access control, and remote access all operate within the same environment. When properly structured, the system is predictable and secure. When it’s not, vulnerabilities are often built in from the start.

Most failures are built in early.
Most security issues are not the result of advanced threats—they come from avoidable design gaps.
Weak Credentials
Weak or reused credentials remain one of the most common openings in connected systems.
Outdated Firmware
Systems that are not updated over time create unnecessary and often preventable exposure.
Unsegmented Networks
When every device shares the same environment, one issue can spread far beyond its starting point.
Poor Remote Access
Improvised or poorly managed remote access can expose system control, activity patterns, and personal data.
Security failures are rarely technical limitations—they’re planning failures.
Security begins with architecture.
A secure system begins with the network architecture.
Security and surveillance
Separated from the rest of the environment for tighter control.
Home automation systems
Organized for stability without unnecessary overlap.
Personal devices
Kept distinct from the systems that run the home.
Guest access
Isolated so convenience does not compromise the environment.

A more secure system is not one with more devices—but one with the right devices, properly deployed.
Reduce exposure. Maintain function.
Every connected device adds complexity. The objective is not maximum connectivity. It is controlled connectivity.
Limit internet-facing hardware
Minimize direct exposure wherever possible.
Prioritize local control
Reduce reliance on cloud services where appropriate.
Choose long-term manufacturers
Use brands with consistent updates and support practices.
Usable systems still need defined control.
Proper access structure keeps the system usable without compromising control.
Unique credentials
Each user and system should have credentials that are not shared.
Multi-factor authentication
Critical access should require another layer of verification.
Defined permissions
Homeowners, staff, and guests should have only the access they need.

Security is not a one-time setting.
Systems require regular updates, periodic access reviews, and ongoing system checks.
Regular updates
Apply device, platform, and network updates deliberately.
Periodic access reviews
Review who has access and whether it is still appropriate.
Ongoing system checks
Confirm the environment remains predictable and serviceable.

Well-designed systems remain stable because they are documented, serviceable, and supported over time.
Private by design—not by afterthought.
Security and privacy should be addressed together. A properly designed system limits unnecessary data collection, reduces reliance on cloud-based services when possible, and keeps control with the homeowner.

Structure comes first.
A secure smart home is structured before devices are selected.
More complexity requires more structure.
Localized control systems
Maintain continuity across larger properties and distributed systems.
Managed remote access
Enable service while keeping access deliberate and controlled.
Secured network infrastructure
Protect the backbone that everything else depends on.
Documented architecture
Support continuity as systems evolve over time.
Security is defined by the design.
Smart home security is defined by how the system is designed—not the devices inside it.
Build the system correctly from the start.
If you're building or upgrading a connected home, we can help structure the system so it remains secure, serviceable, and reliable over time.
Smart Home Security FAQ
What Homeowners Should Know Before Building a Connected System
What makes a smart home “secure”?
A secure smart home is defined by how the system is structured—not the individual devices.
It starts with a properly designed network, controlled access, and systems that are configured to limit exposure. When these elements are coordinated, the home operates predictably and remains secure over time.
Are smart homes more vulnerable than traditional homes?
They can be—if they are not designed correctly.
Most vulnerabilities come from poor setup: weak passwords, unsegmented networks, or unmanaged remote access. With the right structure in place, a smart home can be both secure and reliable.
What is the biggest security risk in most smart homes?
In most cases, it’s not the devices—it’s the network and access strategy behind them.
Flat networks, shared credentials, and outdated systems create unnecessary exposure. These are preventable with proper planning.
Why is network design so important?
All connected systems rely on the network.
A segmented network separates critical systems—like security and automation—from personal and guest devices. This limits how issues can spread and helps maintain system stability.
Do all smart devices need internet access?
No.
In many cases, limiting internet exposure improves security. Systems designed with local control reduce reliance on external services and minimize risk.
How should access be managed across the home?
Access should be structured and intentional.
Each user should have unique credentials, with permissions based on their role. Critical systems should use multi-factor authentication. This keeps the system secure while remaining easy to manage.
Is smart home security a one-time setup?
No.
Security requires ongoing attention. Systems should be updated regularly, access should be reviewed, and performance should be monitored over time.
Without this, even well-designed systems can become vulnerable.
How does smart home security affect privacy?
Security and privacy are closely connected.
A well-designed system limits unnecessary data collection, reduces reliance on cloud services, and keeps control with the homeowner. Privacy should be built into the system—not added later.
What should be prioritized when planning a smart home?
Start with the structure, not the devices.
Network design
System architecture
Access strategy
Long-term support
Once those are defined, device selection becomes straightforward and more reliable.
Are there additional considerations for larger homes?
Yes.
Larger or more complex properties benefit from additional structure, including:
Localized system control
Managed remote access
Secured infrastructure
Documented system design
These steps help maintain reliability as the system grows.
Can an existing system be made more secure?
In many cases, yes.
Improvements often start with network restructuring, credential updates, and system audits. From there, gaps can be addressed without necessarily replacing the entire system.
How do I know if my current system is properly secured?
Signs of a well-structured system include:
Segmented network
Controlled user access
Regular updates and maintenance
Clear system documentation
If these elements are missing, the system may benefit from a review.
What’s the long-term benefit of doing this correctly?
A properly designed system remains:
Predictable
Secure
Serviceable
It continues to perform as expected, without requiring constant fixes or workarounds.
Where should I start?
Start with a clear plan.
A structured approach to system design ensures the technology supports the home—quietly, reliably, and over the long term.